Key Outcomes
Delivered a hybrid cloud/BLE access control system where credentials are managed in the cloud but door unlocks happen via local Bluetooth — ensuring access works even without internet at the door
Supported PAC-BLU Access and Access Mini controllers with up to 3-amp relay control, audit trail logging, and door scheduling for commercial facilities
Turned smartphones into secure access credentials, eliminating the need for physical key cards while maintaining enterprise-grade security and audit compliance
The Challenge
Before partnering with Iottive, Pacific Lock Company was facing several issues:
Internet Dependency for Access Control
Cloud-only access control systems fail when network connectivity is disrupted — precisely when physical security matters most. Pacific Lock needed a system that maintained full functionality at the door regardless of internet availability.
Physical Credential Management Overhead
Traditional key cards and fobs require inventory management, physical distribution, and deactivation when employees leave. For multi-site commercial facilities, this created significant administrative burden and security gaps.
Limited Audit Trail Capabilities
Existing mechanical and basic electronic locks provided no visibility into who accessed which door and when. Facility managers had no way to investigate security incidents or demonstrate compliance with access policies.
Scalable Hardware Support
Pacific Lock’s product line included multiple controller models (PAC-BLU Access and Access Mini) with different relay specifications. The companion app needed to support all variants with a single, consistent interface.
Our Solution
Iottive delivered a comprehensive Bluetooth access control application under a full-cycle product development model.
Bluetooth & IoT Expertise
Engineered a hybrid cloud/BLE architecture: the admin grants access credentials via a cloud portal, the user’s phone downloads and stores those credentials locally, and when the user approaches a PAC-BLU controller, the phone unlocks the door via direct Bluetooth communication — no internet required at the point of entry.
Design Thinking Approach
Mapped the complete access workflow — from admin credential assignment to the moment a user walks up to a door. The UX was optimized for the “approach and unlock” interaction: minimal taps, fast BLE connection, and clear visual/haptic confirmation.
Project Planning & Execution
Delivered in three phases: BLE door unlock and credential storage (Phase 1), cloud credential management and admin portal (Phase 2), audit trail, scheduling, and multi-controller support (Phase 3).
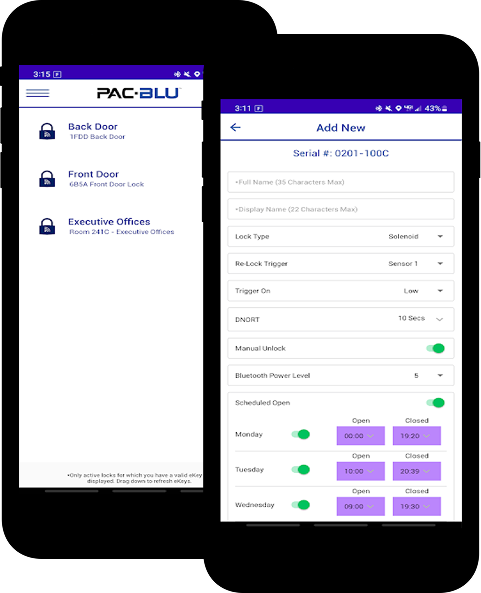
Functionalities Delivered
BLE door unlock with encrypted credential exchange, cloud-based credential provisioning, support for PAC-BLU Access and Access Mini controllers, audit trail with timestamped access logs, door scheduling (time-based access windows), admin management for user permissions, and relay control up to 3 amps.
Implementation Highlights
Hybrid Cloud/BLE Architecture
Designed a split-plane architecture: the cloud manages credentials, permissions, and audit data, while BLE handles the real-time door unlock. Credentials are cryptographically signed in the cloud and verified locally by the controller — no round-trip needed.
BLE Access Protocol
Built a secure BLE communication protocol between the phone and PAC-BLU controllers. The protocol handles device discovery, mutual authentication, credential presentation, and relay activation within a sub-second interaction window.
Credential Lifecycle Management
Implemented full credential lifecycle: issuance from admin portal, secure download to phone, local storage in encrypted keychain, periodic refresh, and remote revocation. Revoked credentials are invalidated on next cloud sync.
Audit Trail & Compliance
Every access event — successful unlock, denied attempt, credential refresh — is logged with timestamp, user identity, door identity, and BLE signal metadata. Logs sync to the cloud for facility manager review and compliance reporting.
Door Scheduling Engine
Built a scheduling system allowing admins to define time-based access windows (e.g., “Building A: Mon– Fri 7AM–7PM, Sat 8AM–1PM”). Schedules are enforced locally on the controller, ensuring policy compliance even when offline.
Multi-Controller Support
Abstracted the BLE communication layer to support both PAC-BLU Access (full-size, up to 3A relay) and Access Mini (compact) controllers through a unified app interface, with hardware specific configuration handled transparently.
Results & Impact
- Zero-internet door unlock via local BLE — access control remains fully functional during network outages
- Physical key card inventory eliminated for facilities using smartphone-based credentials
- Complete audit trail for every access event, supporting security investigations and compliance requirements
- Sub-second unlock experience from approach to door release, matching the speed of traditional proximity cards
- Single app supports multiple PAC-BLU controller models, simplifying deployment for facility managers
“The hybrid approach was non-negotiable for us — our customers cannot accept a door that stops working because the WiFi is down. Iottive engineered exactly that: cloud convenience with local reliability. The BLE unlock is faster than a key card.”
— Gregory B. Waugh, PAC-BLU
Lessons & PAC-BLU
Design for the Disconnected State First
The most critical moment in access control — the door unlock — must work without any network dependency. Designing the offline-first BLE unlock protocol before building cloud features ensured the core promise was never compromised.
Security Is the Product, Not a Feature
In access control, every BLE packet is a potential attack vector. Cryptographic credential signing, mutual authentication, and encrypted communication were foundational architecture decisions, not post development additions.
Optimize for Interaction Speed
Users expect a door to open instantly. BLE connection time, credential verification, and relay activation were each optimized individually, with a combined target of under one second from approach to unlock.
Abstract Hardware Early
Supporting multiple controller variants (Access and Access Mini) from a single app required hardware abstraction from the first sprint. Waiting to add multi-device support later would have required significant refactoring.

Technology
Comprehensive IoT Technology Stack
From devices and connectivity to cloud, apps, and security — we leverage a full-stack IoT ecosystem to build scalable, secure, and future-ready solutions.

Android (Kotlin)
BLE

AWS

Why Iottive’s the Right Partner
- Deep BLE protocol engineering experience — including the sub-second timing and security requirements unique to physical access control
- Proven hybrid cloud/local architecture design that delivers cloud convenience without compromising offline reliability
- Experience integrating mobile apps with commercial hardware controllers, handling the full stack from relay activation to cloud audit trails
