Introduction
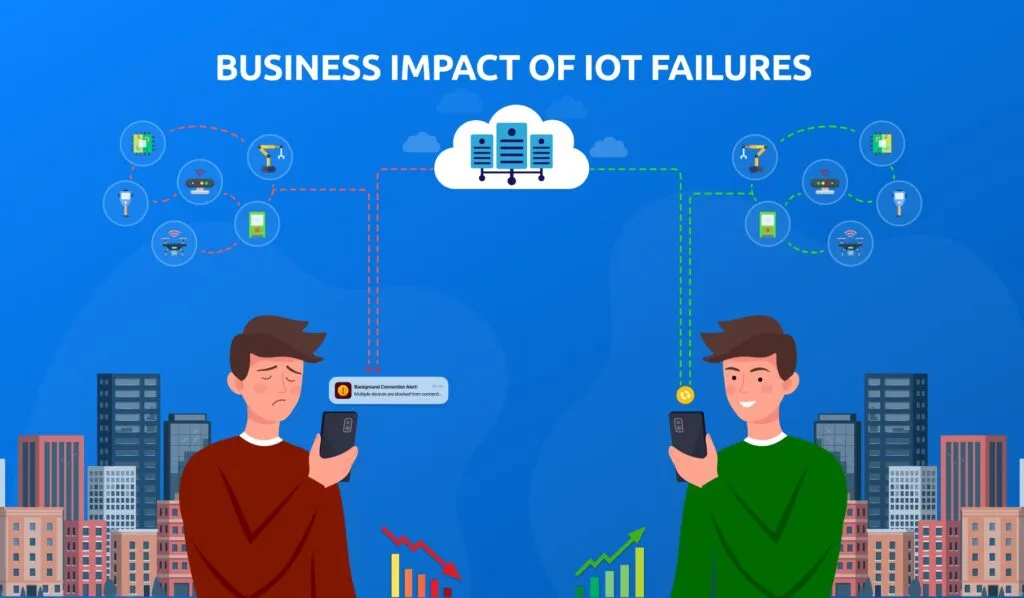
Smart safety devices have become an essential part of modern life, offering solutions for personal security, elder and child care, and pet tracking. Devices such as SOS systems, fall detection sensors, and GPS trackers ensure safety and peace of mind. However, while these devices rely on mobile applications to function effectively, they face an often-overlooked challenge: Background Restrictions.
Both Android and iOS impose strict background process restrictions to optimize battery life and enhance security. While these measures benefit users, they can also interfere with the real-time performance of smart safety devices, leading to delayed alerts, unreliable location tracking, and inconsistent data transmission.
In this blog, we will explore how these Background Restrictions impact various smart safety devices and what solutions can help mitigate these challenges.
Understanding Background Restrictions
To ensure better performance and user experience, mobile operating systems continuously evolve by implementing restrictions on background processes. Some of the key limitations include:
⦁ Background Process Restrictions:
Apps are often put into a suspended state, limiting their ability to run real-time monitoring and alerts.
⦁ Battery Optimization Policies:
Many OS versions restrict background activity to conserve battery life, which can result in delayed or missed notifications
⦁ Location Access Restrictions:
For privacy reasons, continuous GPS tracking is limited, affecting real-time tracking applications.
⦁ Network and Sensor Access Constraints:
Apps may face interruptions in accessing WiFi, Bluetooth, or mobile networks when running in the background, affecting IoT-based safety devices.
To ensure better performance and user experience, mobile operating systems continuously evolve by implementing restrictions on background processes. Some of the key limitations include:
Real-World Impact on Smart Safety Devices Caused by OS Limitations
1. SOS Devices
SOS devices rely on instant emergency alerts to notify caregivers or emergency contacts. However, Mobile OS Background Restrictions can cause:
⦁ Delayed message or call triggers.
⦁ Interruptions in continuous location sharing make it difficult to pinpoint a user’s location in real-time.
⦁ Challenges in keeping the app running actively for emergency response.
2. Remote Fall Detection Systems
Wearable and IoT-based fall detection systems monitor user movements to detect sudden falls. Mobile OS Background Restrictions can lead to:
⦁ Inconsistent data transmission between the wearable and the mobile app.
⦁ Delayed or missed alerts due to background restrictions.
⦁ Limitations in real-time monitoring and response time.
3. Elder and Kids Care Trackers
Devices that track the location of children and elderly individuals depend on seamless GPS and network connectivity. Mobile OS Background Restrictions can result in:
⦁ Delayed location updates, making real-time tracking ineffective.
⦁ App force-closing due to inactivity, leading to loss of monitoring.
⦁ Restricted notifications when an individual exits a predefined safe zone (geofencing).
4. Pet Trackers
Pet tracking devices use GPS and mobile networks to keep owners informed about their pet’s location. Mobile OS Background Restrictions can cause:
⦁ Gaps in GPS tracking due to suspended background services.
⦁ Connectivity issues when the app is not in the foreground.
⦁ Delays in receiving alerts if a pet goes out of a designated safe area.
5. Other IoT-Based Security Devices
Various IoT security devices, such as home monitoring systems and smart alarms, may also face:
⦁ Restrictions in real-time data synchronization.
⦁ Delays in push notifications or security alerts.
⦁ Limited background access to Bluetooth and WiFi networks, impacting device communication.
Workarounds and Solutions
At IOTTIVE, we specialize in overcoming Mobile OS Background Restrictions to enhance the performance of smart safety devices. Our expertise in IoT, BLE, and Connected Devices allows us to implement robust solutions, including:
⦁ Optimizing App Permissions:
Ensuring that apps request and receive necessary permissions, such as “Always On” location access, helps maintain background functionality. Properly configured permissions prevent OS-imposed limitations on critical app features.
⦁ Leveraging Cloud-Based Processing:
Offloading data processing to cloud servers can reduce dependency on mobile background services and ensure seamless communication. This minimizes app activity requirements, improving performance and reliability.
⦁ Using Push Notification Services:
Implementing Firebase Cloud Messaging (FCM) or Apple Push Notification Service (APNS) helps ensure reliable alerts and real-time notifications, even when the app is in the background.
⦁ Battery Optimization Adjustments:
Many operating systems impose aggressive battery-saving policies that limit background activity. Educating users on disabling battery optimization for critical apps, configuring “Unrestricted” battery settings (on Android), and using foreground services ensures continuous monitoring and data transmission.
⦁ Foreground Services & Persistent Notifications:
Keeping essential services running in the foreground by utilizing persistent notifications ensures uninterrupted background operation. This technique is effective for location tracking, SOS alerts, and other critical real-time features.
⦁ Efficient Data Handling & Background Execution Limits:
Smart data compression, batching updates, and limiting resource-heavy background tasks can help apps work within OS constraints while maintaining performance.
⦁ Custom Watchdog Mechanisms:
Implementing in-app watchdog services that detect when background processes are restricted and restarting them automatically helps maintain continuous functionality.
Our tailored IoT solutions help businesses develop reliable, secure, and efficient smart safety applications that remain functional despite OS-imposed constraints.
Conclusion
Mobile OS Background Restrictions can impact the reliability of smart safety devices, leading to delayed alerts and interrupted monitoring. At IOTTIVE, we tackle these challenges with expert IoT solutions, ensuring seamless performance for your smart safety applications.